.
Also, is Ransomware a real threat?
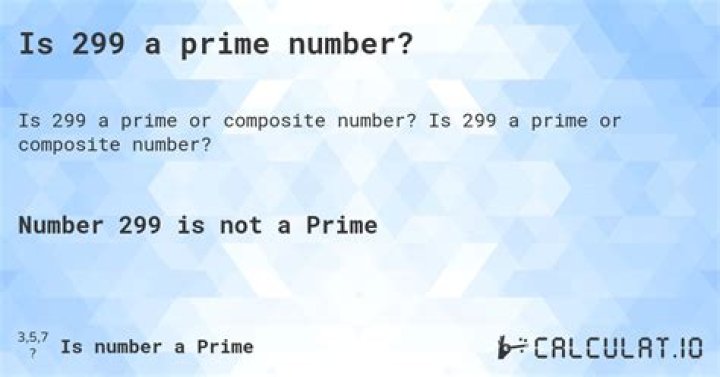
Ransomware is a type of malware from cryptovirology that threatens to publish the victim's data or perpetually block access to it unless a ransom is paid. Starting from around 2012 the use of ransomware scams has grown internationally. There were 181.5 million ransomware attacks in the first six months of 2018.
Likewise, is Ransomware still active? Even when WannaCry first hit, paying the ransom didn't solve anything, but researchers at Sophos have detailed how, despite this, the ransomware still appears active, is still occasionally infecting victims – and sometimes, they're paying the ransom demand.
Also to know, why is ransomware a threat?
Dangers of ransomware Once ransomware infects a user's system, it either encrypts critical files or locks a user out of their computer. The impact of ransomware is immediate, compared to stealthier malware such as those used in an advanced threat attack.
Is CryptoLocker still a threat?
During its spread, any unprotected Windows PC was vulnerable to the trojan. However, CryptoLocker is no longer a threat.
Related Question AnswersCan ransomware be removed?
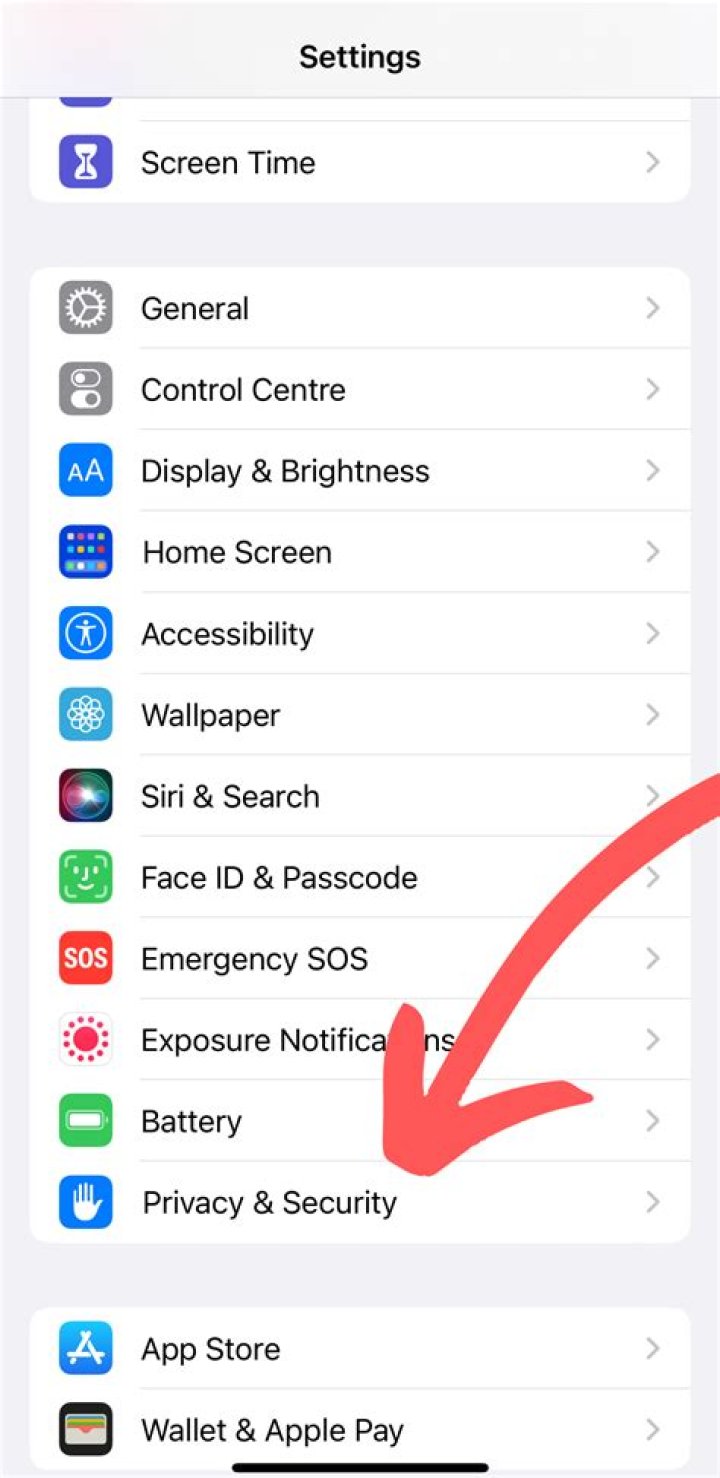
If you have the simplest kind of ransomware, such as a fake antivirus program or a bogus clean-up tool, you can usually remove it by following the steps in my previous malware removal guide. This procedure includes entering Windows' Safe Mode and running an on-demand virus scanner such as Malwarebytes.Should you report Ransomware?
Generally speaking, you could contact the cyber crime cell or Police station in your city/area, and report your case to them. The US Federal Bureau of Investigation is also requesting that ransomware victims contact their local FBI office or file a complaint with their Internet Crime Complaint Center website.How many types of ransomware are there?
twoWhat happens when ransomware attacks?
Once a malicious link is clicked or infected file opened, the ransomware is able to gain a foothold, quickly infiltrating the network and locking up files. In a matter of seconds, malware executables are released into the victim's system where they begin to quickly wreak havoc.What is the latest ransomware attack?
The WannaCry ransomware attack was a May 2017 worldwide cyberattack by the WannaCry ransomware cryptoworm, which targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in the Bitcoin cryptocurrency.What do you do in the event of ransomware?
What You Should Do When Ransomware Attacks- Step 1: Understand Your Situation. You've been infected by malware.
- Step 2: Lock It Down. At this time, all we know is that you're infected.
- Step 3: Shut Down Patient Zero.
- Step 4: Identify the Infection.
- Step 5: Verify Your Backups.
- Step 6: Paying the Ransom.
- Step 7: Decrypting.
How common are ransomware attacks?
Security. Analysis of over 230,000 ransomware attacks that took place between April and September has been published by cybersecurity researchers at Emsisoft and one family of malware accounted for over half (56%) of reported incidents: the 'Stop' ransomware.How common is ransomware?
According to Verizon's most recent data, 2018 Data Breach Investigations Report, ransom attacks were the most prevalent variety of malware in 2017. Verizon's report shows the rapid increase in ransomware as the primary attack vector of all malware. In 2016, ransoms were used for about one-third of all malware attacks.What is an example of ransomware?
Locker is another one of the ransomware examples that Comodo has already taken care of. Locker is similar with cryptolocker. If cryptolocker encrypts the files, lockers ransomware locks the files to deny access to the user and demands $50 to restore the files. It usually targets Word, text, and PDF files.What is a rootkit attack?
Rootkit is a term applied to a type of malware that is designed to infect a target PC and allow an attacker to install a set of tools that grant him persistent remote access to the computer. In recent years, a new class of mobile rootkits have emerged to attack smartphones, specifically Android devices.Can ransomware spread through network?
Yes, it is possible for a Ransomware to spread over a network to your computer. It no longer infects just the mapped and hard drive of your computer system. Virus attacks nowadays can take down the entire network down and result in business disruptions.Can Mcafee remove ransomware?
The Mcafee Ransomware Trojan itself can usually be removed with a security program. However, once the victim's files have been encrypted, they will no longer be recoverable, even if the Mcafee Ransomware Trojan itself is removed from the affected PC.Does Norton protect against ransomware?
Norton 360™ helps protect against ransomware attacks. Add a layer of protection to your data and device. You'll be covered by our Virus Protection Promise2 to help remove any virus or your money back. Not all products, services and features are available on all devices or operating systems.Is Ransomware a social engineer?
How Are They Different? In simple terms, ransomware is a type of malware that encrypts your files, making them inaccessible unless you pay a ransom to the hacker. Social engineering relies on deception to trick a victim into clicking a link or downloading a file that then lets a hacker into their network.How long does it take to recover from ransomware attack?
How long does it take to recover from a ransomware infection? It Takes 33 Hours according to a recent survey by Vanson Bourne of 500 cybersecurity decision makers that was sponsored by SentinelOne. The average victim was hit six times.What is a ransom attack?
Ransomware is a type of malicious software that blocks access to a computer system or data, usually by encrypting it, until the victim pays a fee to the attacker. In many cases, the ransom demand comes with a deadline. If the victim doesn't pay in time, the data is gone forever.What is the most common infection vector for ransomware?
These are the four most common ways ransomware infects its victims.- Phishing Emails.
- Remote Desktop Protocol.
- Drive-By Downloads From a Compromised Website.
- USB and Removable Media.