.
In this manner, how does encryption software work quizlet?
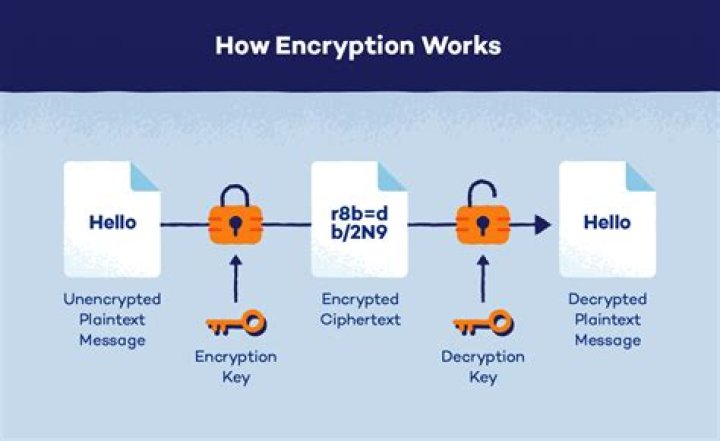
This signature serves to verify that the public key the sender is using for encryption is truly the public key of the intended recipient. An encryption function takes cleartext and a key as input and returns ciphertext.
Secondly, how does encryption software work? Encryption is a process that encodes a message or file so that it can be only be read by certain people. Encryption uses an algorithm to scramble, or encrypt, data and then uses a key for the receiving party to unscramble, or decrypt, the information. In its encrypted, unreadable form it is referred to as ciphertext.
Regarding this, what is encryption quizlet?
Encryption. A security technique designed to prevent access to information by converting it into a scrambled (unreadable) form of text. Decryption. The process of converting encrypted data back to its original form.
Which term is refers to any encryption that uses different keys for encryption and decryption?
Cipher. A cipher is an algorithm that can perform encryption or decryption. A basic example would be to take the plaintext word "code" and encrypt it as a ciphertext using a specific algorithm. Key. The key is the essential piece of information that determines the output of a cipher.
Related Question AnswersWhich type of encryption is the most popular form of email encryption?
Transport-level encryption One of the most commonly used email encryption extensions is STARTTLS . It is a TLS (SSL) layer over the plaintext communication, allowing email servers to upgrade their plaintext communication to encrypted communication.What are the two main types of cryptography?
A cryptographic system typically consists of algorithms, keys, and key management facilities. There are two basic types of cryptographic systems: symmetric ("private key") and asymmetric ("public key"). Symmetric key systems require both the sender and the recipient to have the same key.What encryption means?
The translation of data into a secret code. Encryption is the most effective way to achieve data security. To read an encrypted file, you must have access to a secret key or password that enables you to decrypt it. Unencrypted data is called plain text ; encrypted data is referred to as cipher text.What is data called that is to be encrypted by an encryption algorithm?
Data encryption, also called encryption or encipherment, the process of disguising information as “ciphertext,” or data unintelligible to an unauthorized person. Conversely, decryption, or decipherment, is the process of converting ciphertext back into its original format.How do you store encryption keys?
3 Answers- Use an external Hardware Security Module.
- Tie the encryption to your hardware.
- Tie the encryption key to your admin login (e.g. encrypt the the encryption key with your admin login).
- Type in the encryption key when you start up, store it in memory.
- Store the key on a different server.
What type of encryption algorithm uses two keys to encrypt and decrypt data?
Symmetric keyIn which type of encryption is the same key used to encrypt and decrypt data quizlet?
Symmetric encryptionWhich of the following is also known as encrypted text?
Encrypted text is also known as cipher text. Encryptio is the translation of data into a secret code. It is the most effective way for achieving the security of data. In general terms, unencrypted data is also known as plain text whereas encrypted data is alos called as cipher text.What is meant by symmetric encryption?
Symmetric encryption is an encryption methodology that uses a single key to encrypt (encode) and decrypt (decode) data. It is the oldest and most well-known technique for encryption. The secret key can be a word, a number, or a string of letters, and it's applied to a message.What is a Hash CIW?
An encryption method in which two keys (a private key and a public key) are used to encrypt and decrypt a message. Also known as public-key encryption. Hash encryption. An encryption method in which hashes are used to verify the integrity of transmitted messages. Also known as one-way encryption.What is a patch quizlet?
Patch. A piece of software designed to update or fix problems with a computer program or its supporting data.What is spyware quizlet?
Spyware. A type of Malware that locates and saves data from users without them knowing about it. Virus. A piece of code that is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data.What is encryption with example?
verb. Encryption is defined as the conversion of something to code or symbols so that its contents cannot be understood if intercepted. When a confidential email needs to be sent and you use a program that obscures its content, this is an example of encryption.What is encryption used for?
Encryption refers to any process used to make sensitive data more secure and less likely to be intercepted by those unauthorized to view it. There are several modern types of encryption used to protect sensitive electronic data, such as emails, files, folders and entire drives.Why is encryption needed?
Encryption is important because it allows you to securely protect data that you don't want anyone else to have access to. Espionage uses encryption to securely protect folder contents, which could contain emails, chat histories, tax information, credit card numbers, or any other sensitive information.How do you decrypt?
Press "Windows-E" on your keyboard and navigate to location of the file you wish to decrypt. Right-click the file name and click "Properties." Click the "Advanced…" button on the General tab under the Attributes section. Uncheck the box next to "Encrypt Contents to Secure Data," then click the "OK" button.What is the best encryption software?
Top 12 Best Free File Encryption Software for Computer in 2019- Gihosoft File Encryption (Windows) Gihosoft File Encryption is one of the best file encryption software for PC.
- VeraCrypt (Windows/OS X/Linux)
- 7-Zip (Windows/OS X/Linux)
- AxCrypt (Windows)
- BitLocker (Windows)
- LastPass.
- FileVault2.
- DiskCryptor.